Microsoft Confirms Exploited Exchange OWA Vulnerability as CVE-2026-42897
Microsoft has disclosed CVE-2026-42897, a high-severity Exchange Server Outlook Web Access vulnerability affecting on-premises deployments, with mitigation available while a permanent fix is pending.
Microsoft Confirms Exploited Exchange OWA Vulnerability as CVE-2026-42897
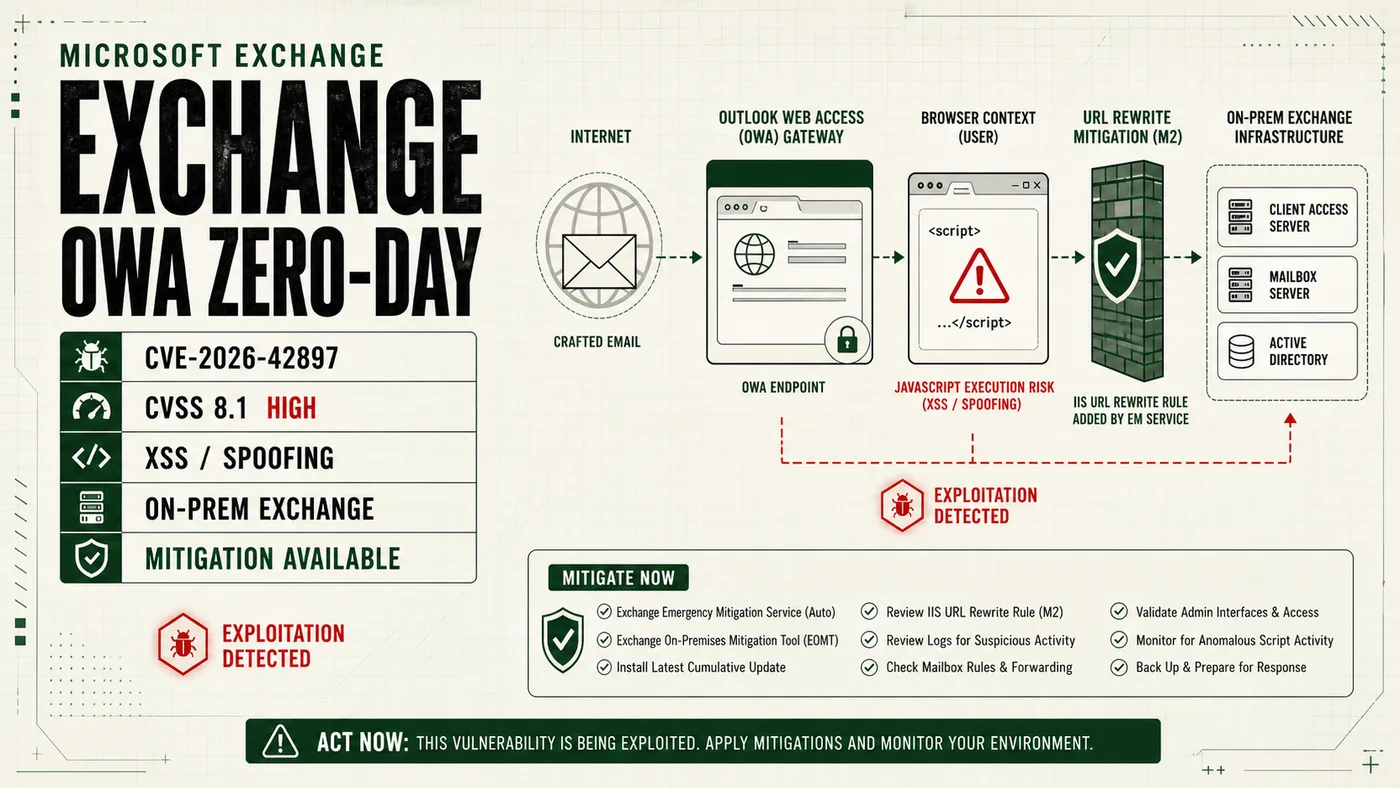
Microsoft has disclosed CVE-2026-42897, a high-severity Microsoft Exchange Server vulnerability affecting Outlook Web Access on on-premises deployments. The issue is now tracked by Microsoft and vulnerability databases, carries a CVSS v3.1 score of 8.1, and has been reported as exploited while a permanent security update is still pending.
The disclosure changes the posture for defenders. Earlier reports framed the Exchange issue as unverified, but Microsoft published guidance on May 14, 2026, and described an Exchange Outlook Web Access vulnerability that can be triggered through a specially crafted email when a user opens the message in OWA and certain interaction conditions are met.
| Item | Current status |
|---|---|
| Identifier | CVE-2026-42897 |
| Product | Microsoft Exchange Server Outlook Web Access |
| Severity | High |
| CVSS v3.1 | 8.1 |
| Attack class | Cross-site scripting / spoofing |
| Attack vector | Network |
| User interaction | Required |
| Affected deployments | On-premises Exchange Server, including Exchange Server Subscription Edition, 2019, and 2016 |
| Exchange Online | Not reported as affected |
| Patch availability | Permanent fix pending as of May 15, 2026 |
| Mitigation | Exchange Emergency Mitigation Service or Exchange On-premises Mitigation Tool |
Exchange remains one of the most sensitive systems in many enterprise networks. It handles email, calendar data, authentication-linked workflows and business communications, making exposed servers attractive targets for espionage groups, ransomware operators and financially motivated intrusion crews.
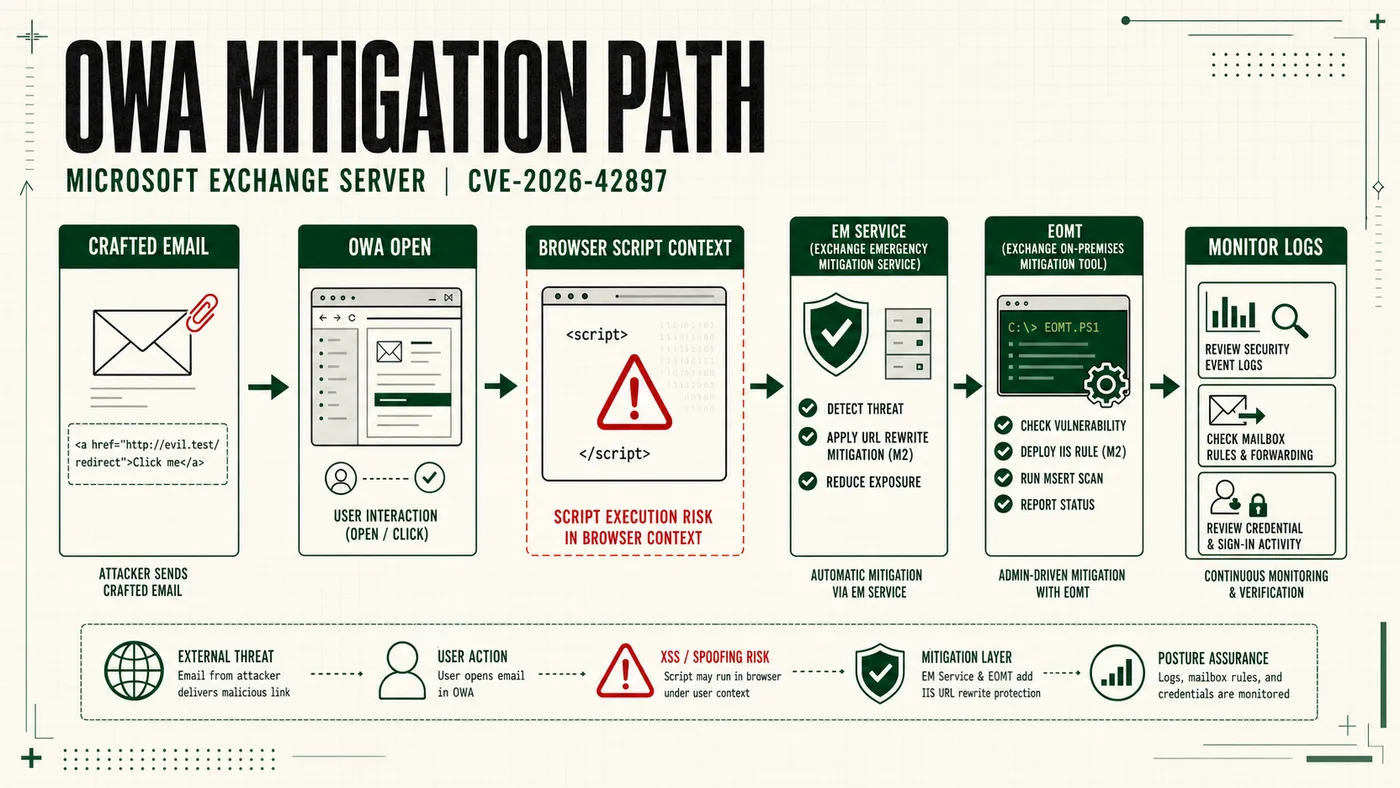
The reported exploit path is not a classic unauthenticated remote code execution chain against the server itself. Microsoft and vulnerability databases describe improper neutralization of input during web page generation. In practical terms, a crafted message viewed through OWA can create a browser-context script execution risk, which can support spoofing and abuse of the user session if the interaction requirements are met.
That distinction matters. Defenders should not treat this as a reason to ignore the issue, but they should tune response around the actual exposure: Outlook Web Access, crafted email content, browser-side execution, mailbox/session abuse, and whether Microsoft mitigation has reached all on-premises Exchange systems.
Administrators should first confirm whether Exchange Emergency Mitigation Service is enabled and whether mitigation M2 has been applied. Microsoft has also pointed administrators to the Exchange On-premises Mitigation Tool where automatic mitigation is unavailable or unsuitable.
Immediate defensive measures include:
- Confirm that Exchange Emergency Mitigation Service is enabled and current.
- Verify whether mitigation M2 has been applied to affected Exchange servers.
- Use the Exchange On-premises Mitigation Tool where EM Service cannot apply the mitigation.
- Restrict external access to Outlook Web Access and Exchange administrative interfaces where operationally feasible.
- Review recent successful and failed authentication attempts for OWA users.
- Inspect Exchange web and transport logs for unusual message access patterns.
- Monitor for suspicious mailbox rule changes, external forwarding and delegated access changes.
- Review privileged account activity and group membership changes.
- Confirm endpoint detection coverage on Exchange hosts.
- Validate backups and restoration procedures.
- Prepare emergency patching plans for the permanent Microsoft update.
Security teams should pay close attention to behavior often associated with Exchange and mailbox compromise, especially where it appears on servers exposed to the public internet. Suspicious patterns may include unusual OWA access, unexpected mailbox forwarding rules, anomalous sign-ins from unfamiliar infrastructure, permission changes, high-volume mailbox access, or user reports of unexpected content rendering in OWA.
A basic triage workflow can help administrators review recent activity while avoiding untrusted tools.
# Review recent PowerShell activity
Get-WinEvent -LogName "Windows PowerShell" -MaxEvents 200 |
Select-Object TimeCreated, ProviderName, Id, Message
# Review recent security log activity
Get-WinEvent -LogName "Security" -MaxEvents 500 |
Select-Object TimeCreated, Id, ProviderName, Message
Organizations that identify suspicious activity tied to OWA or Exchange mailboxes should treat the affected accounts and systems as potentially exposed. Response steps should include preserving logs and forensic evidence, reviewing mailbox rules and permissions, rotating exposed credentials, checking privileged access, and confirming that mitigation has been applied before returning the environment to normal operating posture.
The lack of a permanent patch does not mean defenders are without options. The priority is to verify mitigation coverage, reduce unnecessary exposure, monitor for mailbox and OWA abuse, and be ready to apply Microsoft’s final security update when it becomes available.
Sources
- Microsoft Exchange Team, "Addressing Exchange Server May 2026 vulnerability CVE-2026-42897," May 14, 2026: https://techcommunity.microsoft.com/blog/exchange/addressing-exchange-server-may-2026-vulnerability-cve-2026-42897/4518498/replies/4519822
- Microsoft Security Update Guide, CVE-2026-42897: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-42897
- Tenable CVE record for CVE-2026-42897: https://www.tenable.com/cve/CVE-2026-42897
- Help Net Security, "Unpatched Microsoft Exchange Server vulnerability exploited (CVE-2026-42897)," May 15, 2026: https://www.helpnetsecurity.com/2026/05/15/exchange-server-cve-2026-42897-exploited/